
Story
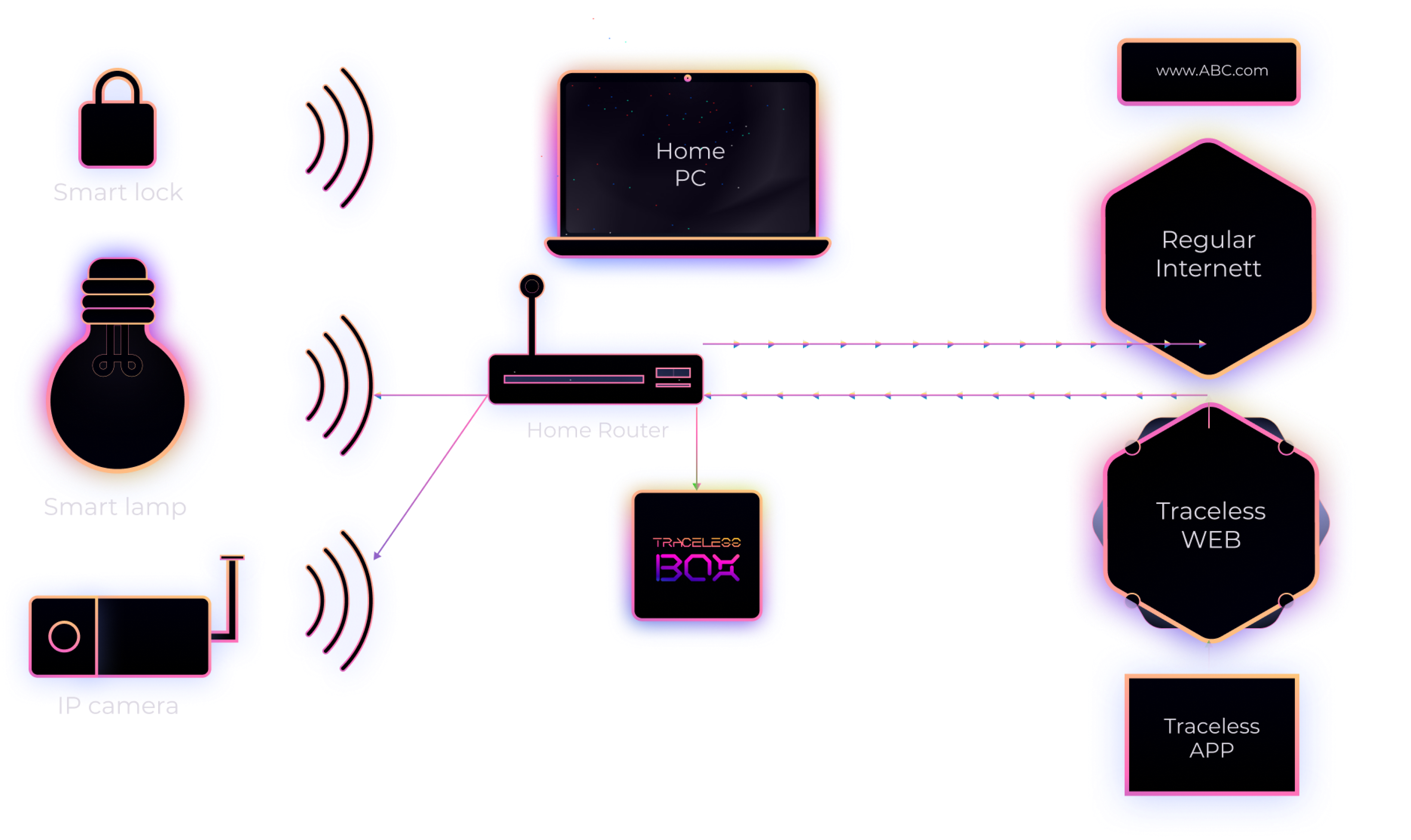
The “Box” protects IOT devices located in the local network from external threats by hiding the IP addresses of initiator and addressee of every communication session and routing them through the decentralized network.
-
Protection for your IOT devicesThe “Box” protects IOT devices located in the local network from external threats by hiding the IP addresses of initiator and addressee of every communication session and routing them through the decentralized network.
-
Privacy for youBoth parties of every communication session remain unknown and are connected to each other through the multiple intermediaries, without any of them knowing the origin and destination address.
-
Post-Quantum encryption for your trafficPost-quantum encryption optionally applied to traffic and to the locally stored information to protect it from future threats.

Protection for IOT devices
-
IOT gadgets can be accessed with the assistance of the traceless app“Traceless App” is a part of the ecosystem and it is introduced to let users securely communicate with IOT gadgets while outside of the home network.
-
Hackers can't find them behind the Traceless BoxNone of the electronics accessible to user can be seen by others, as they can be accessed only through the known decentralized address that is dynamically changed.
-
Even the cheapest electronics become fully protectedBluetooth, ZigBee, and WiFi enabled devices – All can be connected to the “Box” and controlled by user from the “Traceless App”, which is convenient, secure, and allows creating various interaction scenarios.
Privacy for you

Post-Quantium encryption for your traffic

-
Have your connections encrypted against quantum computersAs an additional security option, you may elect to have your traffic encrypted against quantum computers that will inevitably become a part of our lives soon.


